After I installed Java 8 on my main notebook, I had the need to get on an ILOM for an ODA rebuild in the lab, and boy was I surprised with this error!
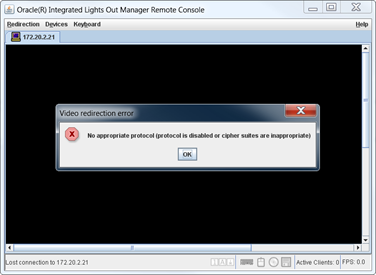
So, after a little research on the error, I figured out that the ILOM uses SSLv3. On that note, Wireshark is a great FREE sniffer. You can grab a copy from here. https://www.wireshark.org/
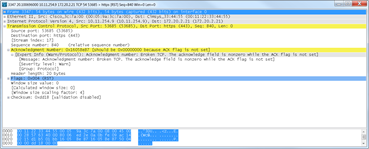
What I saw here, is the ACK not being sent from my system. But the packets were being received. So I dug around a little and discovered that in JDK 8u31, JDK 7u75 and JDK 6u91 SSLv3 is disabled by default to address the SSL V3.0 Poodle Vulnerability. Details on that are here; http://www.oracle.com/technetwork/topics/security/poodlecve-2014-3566-2339408.html
Being it was a weekend, my quick fix is to enable SSLV3 on the Java Client. To do this, locate the java.security file ( On windows look in c:\Program Files (x86)/Java/jre1.8.0_45/lib/security or something similar ) and comment out the line;
jdk.tls.disabledAlgorithms=SSLv3
So, it should now look something like this;
# See the specification of "jdk.certpath.disabledAlgorithms" for the
# syntax of the disabled algorithm string.
#
# Note: This property is currently used by Oracle's JSSE implementation.
# It is not guaranteed to be examined and used by other implementations.
#
# Example:
# jdk.tls.disabledAlgorithms=MD5, SSLv3, DSA, RSA keySize < 2048
#jdk.tls.disabledAlgorithms=SSLv3
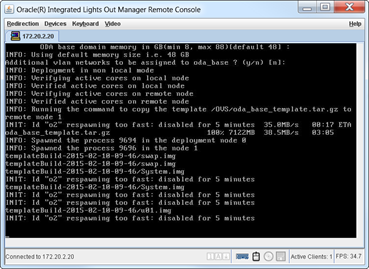
While, this is not the perfect fix, it will get you through an install.
Now I can get back to the ODA rebuild!
This solved my issue. Thank you for the detailed writeup.
Thank you Erik! I had the exact same problem and this saved me a lot of grief… at least a long car drive to the data center. Cheers!
Very helpful, thanks!
Thanks! Helped with an old console I needed to access.
It works for me. Thanks a lot.
It helped . thanks a lot
Thanks A LOT, I had the same issue on a SunFire x4550.
Since I’m using IcedTea I’m posting a link for changing the disabledAlgorithms value there, but it’s very similar:
https://www.crc.id.au/2015/01/31/java-update-broke-the-dell-drac-5-remote-management-cards/
http://www.ca.com/us/services-support/ca-support/ca-support-online/knowledge-base-articles.tec0000001472.html
I love it when someone copy’s my steps… a year latter, and forgets to give credit!
Thanks CA! 🙂
Great article !!!
Worked like a charm !!!
works for me. Thanks